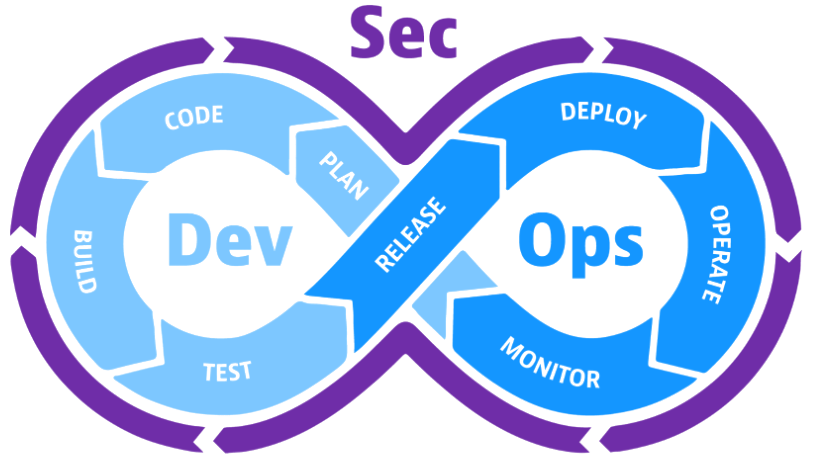
IT Security, possible!

Comprehensive Assessments for Compliance and Resilience
Robust security in cloud environments is indispensable for protecting sensitive data, maintaining regulatory compliance, mitigating cyber threats, ensuring business continuity, and navigating the unique challenges posed by the dynamic and shared nature of cloud computing. Organizations must adopt a comprehensive and proactive approach to security to fully leverage the benefits of cloud technologies while minimizing risks.
EZIT will ensure: your cloud compliance assessment, security controls gap assessment, and vulnerability assessment.
- Assurance of regulatory compliance.
- Evaluating the effectiveness of current controls.
- Pinpointing gaps and vulnerabilities.
- Providing actionable recommendations to address identified gaps.
- Strategies for implementing and enhancing security controls.
- Creating comprehensive reports on identified vulnerabilities.
- Prioritizing vulnerabilities based on risk.
- Collaborating with clients on remediation strategies.
Strengthen Your Cyber Defenses with Our Breach and Attack Simulation

In today’s rapidly evolving digital landscape, cybersecurity is not a luxury; it’s a necessity. Stay one step ahead of cyber threats with our cutting-edge Breach and Attack Simulation (BAS) services. As a leading provider, we empower organizations to proactively assess, identify, and remediate potential vulnerabilities, ensuring robust cybersecurity defenses.
Validate your defenses:
- Evaluate if your tools accurately detect ransomware and see just how far it can spread.
Realistic Simulations:
- Our BAS services go beyond traditional testing methods. We employ realistic simulations of cyber threats, providing a comprehensive evaluation of your organization’s security posture.
Continuous Monitoring:
- Cyber threats don’t rest, and neither do we. Benefit from continuous monitoring to detect and address emerging vulnerabilities, keeping your defenses resilient against evolving cyber threats.
Customized Scenarios:
- Tailored to your unique business environment, our BAS services create custom attack scenarios that mimic real-world threats, helping you understand and mitigate risks specific to your organization.
Actionable Insights:
- Receive detailed reports and actionable insights that not only highlight vulnerabilities but also provide recommendations for strengthening your security infrastructure.
Training and Awareness:
- Elevate your team’s cybersecurity awareness through targeted training modules derived from BAS findings. Empower your staff to recognize and respond effectively to potential threats.

Strengthening Your Defenses
The increasing threat landscape and the critical need for robust cybersecurity measures. We are here to provide VAPT services, emphasizing the proactive approach to identifying and addressing vulnerabilities.
Vulnerability Assessment:
- Identifying potential vulnerabilities and weaknesses.by performing vulnerability assessment of network, applications and endpoints
- Creating comprehensive reports on identified vulnerabilities.
- Prioritizing vulnerabilities based on risk levels.
- Recommendations for remediation and risk mitigation.
Penetration Testing:
- Simulating real-world attack scenarios to uncover vulnerabilities through black-box, white-box, grey-box testing methodologies
- Conducting controlled simulated attacks on systems and applications.
- Providing detailed reports on successful penetration testing scenarios.
- Collaborating with clients to develop and implement remediation strategies.
- Aligning VAPT services with industry-specific compliance standards.
- Assisting clients in meeting regulatory requirements.
- Providing documentation for regulatory audits.
Detect & Safeguard Your Digital Footprint

Recap of the importance of reconnaissance in maintaining a secure digital footprint.
Encouragement for businesses to prioritize understanding and securing their online presence.
Surface Web Reconnaissance:
- Surface Web Reconnaissance:
- Identifying information that may pose security risks.
- Utilizing advanced search techniques to uncover publicly accessible data.
- Analyzing information from various online sources.
- Providing comprehensive reports on publicly available information.
- Identifying potential risks associated with the exposed data.
Dark Web Reconnaissance:
- Explaining the significance of monitoring activities on the dark web.
- Identifying any compromised credentials or sensitive information for sale.
- Developing response plans for potential incidents identified on the dark web.
- Collaborating with clients to mitigate risks and secure sensitive data.
- Providing personalized reconnaissance services based on the industry and specific threats.
- Tailored analysis to address unique business risks.

Navigating GDPR Compliance with Expertise
We provide DPO as a Service through our certified legal practitioners. DPOaaS is valuable option for organizations that do not have the in-house resources to hire a full-time DPO. We offer a wide range of services under our DPOaaS program.
- Conducting a thorough analysis of data processing activities.
- Creating a comprehensive data inventory.
- Conducting PIAs to identify and mitigate privacy risks.
- Ensuring compliance with GDPR’s risk-based approach.
- Developing incident response plans for data breaches.
- Providing guidance in the event of a security incident.
- Maintaining detailed records of data processing activities.
- Providing reports for regulatory authorities and internal stakeholders.
Regulatory Liaison:
- Serving as a point of contact for regulatory authorities.
- Handling communications and submissions related to GDPR compliance.
Legal Consultation:
- Providing legal advice on data protection matters.
- Assisting in interpreting and navigating evolving GDPR regulations.
Why Choose EZIT
With a team of experienced cybersecurity experts, state-of-the-art technology, and a commitment to excellence, we are your trusted partner in fortifying your digital defenses. Our Cloud security services, BAS services, VAPT services, Reconn services and DPO services are designed to adapt to the ever-changing threat landscape, providing you with the confidence to navigate the digital realm securely.
Moneyback
Gurentee
Technical
Support
We develops strategic software solutions for businesses.
establishment
worldwide
client base
rating